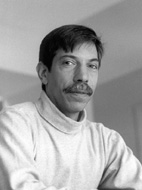
Fred B. Schneider
Professor
fbs@cs.cornell.edu
Ph.D. SUNY Stonybrook, 1978
http://www.cs.cornell.edu/fbs/
Honors
University Activities
Professional Activities
Lectures
Publications
Patents
Research this past year continued into techniques to support the construction of concurrent and distributed systems for high-integrity, mission-critical settings.
Inlined reference monitors remain a promising approach for enforcing security policies, especially the fine-grained policies needed when the Principle of Least Privilege is employed to protect against hostile mobile code. This past year, our PSLang (Policy Specification Language) and PoET (Policy Enforcement Toolkit) toolsdeveloped with Ph.D. student Ulfar Erlingssonwere demonstrated in two settings. First, we were able to show how Java2s stack inspection security policy can be enforced with overhead that is competitive with kernel-based reference monitors. Second, Cornells Digital Library has started using PSLang/PoET for imposing rights management and preservation policies on digital objects in their repository.
Our investigations into interactions between security and fault-tolerance (joint work with Lidong Zhou and Robbert van Renesse) also continued. We have deployed our replicated certification authority at four sites on the Internet, and we are now making detailed performance measurements. The service supports on-line revalidation of bindings and is designed to resist a broad collection of denial of service attacks.
Professor-at-Large, University of Tromsoe, Tromsoe, Norway (19962001).
Daniel M. Lazar 29 Excellence in Teaching Award, 2000.
Chair: Computing Facilities Committee, Computer Science Department.
Member: Faculty Advisory Board in Information Technology (FABIT);
University Academic Freedom Committee; Duffield Hall Design Committee.
Director: AFRL/Cornell Information Assurance Institute.
Editor-in-chief: Distributed Computing.
Editor: Information Processing Letters; High Integrity Systems; Annals of Software Engineering; ACM Computing Surveys.
Co-managing Editor: Texts and Monographs in Computer Science, Springer-Verlag.
Program Committee Member: 1st International Symposium on Agent Systems and Applications (ASA99); NORDSEC 2000 5th Nordic Workshop on Secure IT SystemsEncouraging Co-operation.
Member: Award committee for Principles of Distributed Computing Influential Paper; JavaSoft Security Advisory Committee; deCode Genetics Security Advisory Board; Eweb UniversityCom Board of Advisors; FAST ASA Technical Advisory Board.
Member: IFIP Working Group 2.3 (Programming Methodology).
Trust in Cyberspace. Keynote lecture. Cornell Public Policy and Law Symposium, Ithaca, NY. July 1999.
. Federal Communications Commission, Washington, D.C., October 1999. Advanced Systems Seminar. University of Oslo, Oslo, Norway, August 1999.
. Introduction: Unifying the field of systems?
. Multiplexing to handle performance mismatches.
. Replication management: Application to Agent Integrity.
. The Gold Standard for Security.
. Language Based Security: A new approach.
. Trust in Cyberspace.
Radio interview. Live On Line News, San Diego, CA, August 1999.
Mobile Agent Miracles and Graveyards. Panelist, ASA/MA 99, Palm Springs, CA, October 1999.
Fault-tolerance Issues For Mobile Agents. Dartmouth Workshop on Transportable Agents, Palm Springs, CA, October 1999.
Enforceable Security Policies. Qualcomm Distinguished Lecture Series, Dept. of Computer Science, University of California at San Diego, CA, October 1999.
Reinventing Security for Trust in Cyberspace. Banquet speaker. Beyond Moores Law: Opportunities and Threats from Future, Ubiquitous, High-Performance Computing; Center for Global Security Research, Lawrence Livermore National Laboratory, December 1999.
Radio interview. All Things Considered, National Public Radio, December 17, 1999.
Defense Against Malicious Content and Code. ISAT Meeting on Mobility and Security, Software Engineering Institute, Pittsburgh, PA, January 2000.
It Depends on What You Pay. Malicious Code Infosec Science and Technology Study Group, San Antonio, TX, January 2000.
SASI Enforcement Of Security Polices: A Retrospective. Information and Survivability Conference and Exposition (DISCEX00), Hilton Head, SC, January 2000.
Containment and Integrity of Mobile Code. Intrusion tolerant systems investigators meeting, Aspen, CO, February 2000.
The Non-technical Take on Computing System Trustworthiness. Holy Cross University, Worcester, MA, March 2000.
. Jones Seminars on Science, Technology and Society. Dartmouth College, Hanover, NH, April 1999.
Secret Sharing Tutorial. University of Tromso, Tromso, Norway, March 2000.
AFRL/Cornell Information Assurance Institute. Air Force Rome Laboratories, Rome, NY, April 2000.
Overview of Mobile Code Security. Air Force Rome Laboratories, Rome, NY, April 2000. Network Information System Trustworthiness. Short Course on Competitive Strategies for E-Commerce, Johnson Graduate School of Management, Ithaca, NY, April 2000.
Radio interview. Weekend All Things Considered, National Public Radio, May 6, 2000.
Are There Systems Principles or Only Systems Principals? Invited speaker. In Pursuit of Simplicity, A Symposium Honoring Professor E.W. Dijkstra. Austin, TX, May 2000.
Open Source in Security: Visiting the Bizarre. Panelist. IEEE Symposium on Security and Privacy. Oakland, CA, May 2000.
In-lined Reference Monitors. InCert Software, Cambridge, MA, May 2000.
Building trustworthy systems: Lessons from the PTN and Internet. IEEE Internet Computing, 3, 5 (November-December 1999), 6472 (with S. Bellovin and A. Inouye).
SASI enforcement of security policies: A retrospective. Proceedings of the New Security Paradigm Workshop, Caledon Hills, Ontario, Canada, Association for Computing Machinery, 1515 Broadway, NY (September 1999), 8795 (with U. Erlingsson).
SASI enforcement of security polices: A retrospective. Reprinted in DARPA Information and Survivability Conference and Exposition (DISCEX00), Hilton Head, SC, IEEE Computer Society, Los Alamitos, CA (January 2000), 287295 (with U. Erlingsson).
IRM enforcement of Java stack inspection. Proceedings 2000 IEEE Symposium on Security and Privacy, Oakland, CA, IEEE Computer Society, Los Alamitos, CA (May 2000), 246255 (with U. Erlingsson).
Open source in security: Visiting the bizarre. Proceedings 2000 IEEE Symposium on Security and Privacy (Oakland, CA, IEEE Computer Society, Los Alamitos, CA (May 2000), 126127.
Interview with Fred B. Schneider. Distributed Systems Online. http://www.computer.org/channels/ds.
Transparent fault tolerant computer system. United States Patent 5,968,185, October 19, 1999. Co-inventors: T. Bressoud, J.E. Ahern, K.P. Birman, R.C.B. Cooper, B. Glade, and J.D. Service.